TechTakeOver Blog
Imagine automating repetitive tasks, managing thousands of systems remotely, or digging deep into...
In a world where cyber threats evolve faster than traditional defenses, trusting anything by default...
In a world where cyber threats are evolving faster than ever, traditional perimeter-based security...
Whether you’re debugging code, managing servers, or automating tasks, mastering the Linux...
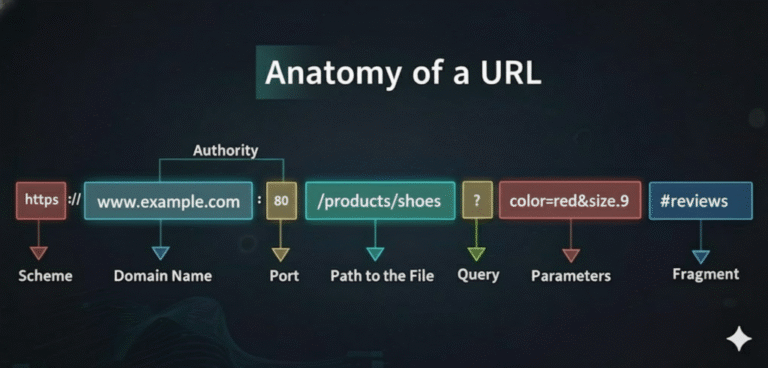
Every time you click a link, you’re trusting a string of characters to take you somewhere safe...
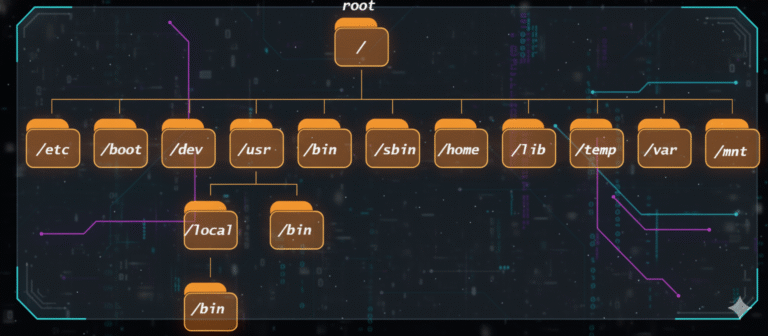
Ever wondered why Linux directories look so cryptic? Or why everything starts from a single slash /?...